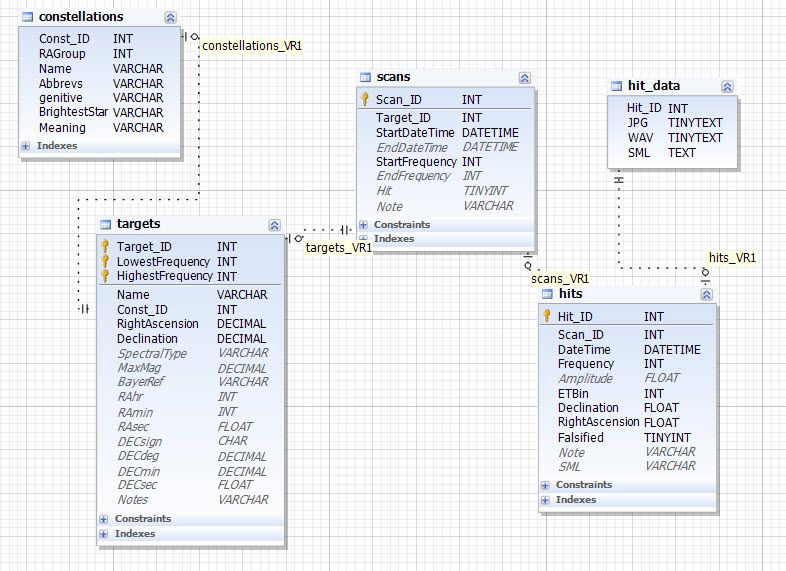
SETI Database Layout
The SETI database used in SETI Net is organized according to the following rules.
Database Dictionary
- Search- The collection of all Targets. The complete Search is held in the database SETI. There is one Search instance only.
- Targets - The Search is made up of one or more Target instances. Each is Target is a Star or other object from the list of objects available to SETI Net. The Target is held constant through out the Search. A single Target will start at the lowest of all Scan frequencies and end with the highest of all Scan frequencies (see the next figure). Scans may overlap in Start/End frequency. When a Scan is added to a Target the Lowest and Highest frequency of the Target is modified accordingly.
- Scan - Each Target is made up of one or more Scans. Each Scan contains a Start Frequency and an End Frequency and zero or one Hits. The frequency increases due to frequency jumps or operator action
- Hit - If a signal is detected during the processing of a Scan a Hit is created. The recording system comes on and the JPG and WAV files are saved. The operator enters falsification notes and then manually ends the Scan and sets the falsified condition for the Hit (Open hit, Antenna Movement, Operator Error, Huge and Ugly or Other Good reason).
- Hit Data - Each Hit generates one or more JPG files and one or more WAV files. The JPG is a visual image of the waterfall buffer used to extract signals. The WAV file is the raw PCM data collected directly from the sound system. Each WAV and JPG file also contains an SML instance collected as the file was created.
- SML - The SETI Markup Language (SML) collects the engineering parameters about the station at the time of the hit. It contains a complete description of the station configuration (time, pointing angles, frequency and other engineering settings) when the file was created. . Each SML instance is held in the files, JPG and WAV, that are generated during a Hit.
The latest database is available here:
Your own database
If you plan to build your own SETI Net station you will need to install a MySQL database on your own machines localhost. This is used to mirror the remote website database.
A helpful video can be found here for the process.
Example: Database Symbols
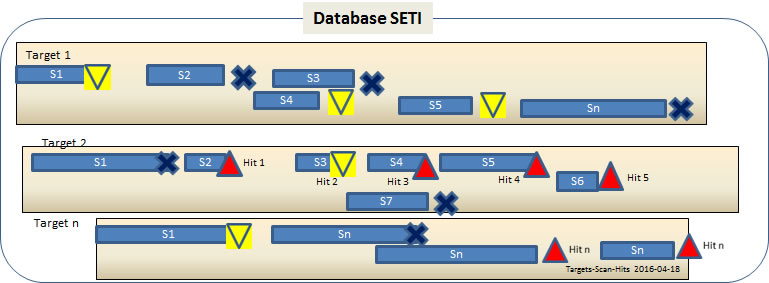
Example: This figure shows activity on three target stars.
For each target in this figure the X axis represents frequency, the Y axis time.
Target 1 shows 6 scans S1, S2 and S3 appear to have happened on the same day. S4 the next day and S5 and S6 a later day yet.
Target 2 shows seven scans completed with a total of five hits (the red and yellow diamonds). The hit that terminated S3 has been falsified and and has been updated with a yellow diamond. On this target four hits remain un-falisifed open hits(red diamond)to indicate more work is required. Two of the scans, the first and the last, were terminated by operator intervention or some other anonymity (black 'X').
Target 3 shows 4 scans on two different days.
Database Organization